At the RSA Conference in San Francisco, Stephen McDermid, Chief Security Officer, EMEA region, for Okta, outlines how the convergence of regulatory pressure, evolving cyber threats, and the rise of agentic AI is reshaping enterprise security. He emphasizes that organizations must move beyond purely technical controls toward a continuous, organization-wide security culture, while prepping for a future where AI agents operate at massive scale.
In this environment, identity becomes the central control layer—governing not just people, but machines, services, and autonomous agents. McDermid argues that companies must adopt strong governance, visibility, and lifecycle management early, or risk losing control as AI adoption accelerates.
Core Takeaways
Regulation Drives Visibility and Trust: In highly regulated regions like EMEA, organizations must provide clear visibility into how data is stored, accessed, and used, making transparency and control foundational to modern security strategies.
Security Culture Is the Strongest Control: Technology alone is insufficient; organizations must build a continuous, organization-wide security culture where employees understand threats, recognize anomalies, and know how to respond.
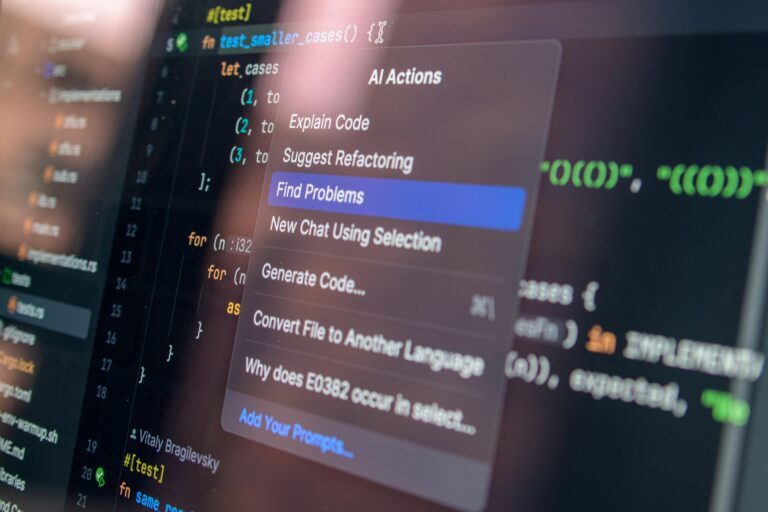
Identity Becomes the AI Control Plane: As AI agents proliferate, identity systems must govern them just like human users, enabling authentication, validation, and real-time control—including the ability to shut down rogue agents instantly.
ISPM Reveals Hidden Risk: Identity Security Posture Management helps organizations uncover forgotten accounts, weak credentials, and unmanaged identities across systems, exposing risks that often go undetected in complex environments.
Key Quotes
Security Culture Is Never Finished
“[Security] is a never ending goal. The pace of the threats that we are seeing, they’re moving so fast that yes, you can have technical controls, technology controls, process controls, but ultimately the best control is the people within your organization. That’s why it’s so important to have a strong culture where people understand what good looks like.”
“When people recognize what good looks like, they become much better at detecting what bad looks like and how to respond. That culture has to be reinforced continuously. There isn’t an end goal—you’re constantly evolving and adapting based on what’s happening in the real world.”
AI Requires Governance, Not Just Adoption
“If you’re not embracing AI, you’re going to have to react to it. What we want to do is give customers the control and governance to use AI safely. It’s not about AI for AI’s sake—it’s about helping the business achieve its goals in a secure and governed way.”
“That means having visibility, control mechanisms, and even something like a kill switch. If something goes wrong, how do you stop it? How do you make sure it doesn’t share the wrong data or take the wrong action? That control layer is critical.”
AI Agents Introduce Identity at Massive Scale
“AI agents will have identities, whether they’re acting on behalf of a person, a company, or a service. And the risks we see today—credential-based attacks, weak authentication—those don’t go away. They extend directly into the world of AI.”
“The real question becomes: how do you know that the agent you’re interacting with is the one you think it is? Verifiable digital credentials will be key. As agents become more common, establishing trust in their identity will be absolutely essential.”
ISPM Exposes What Organizations Miss
“Businesses are constantly transforming—new applications, new infrastructure, new data silos—and identities are created everywhere. The challenge is that many of these identities are forgotten over time, but the risks remain.”
“When customers use ISPM (Identity Security Posture Management), it’s often an eye opener. They discover accounts they didn’t know existed, weak passwords with admin rights, or credentials that were never rotated. It shines a light on hidden risk and allows organizations to bring those identities back under control—or remove them entirely.”