At the RSA Conference in San Francisco, RSA President and Chief Product and Strategy Officer Jim Taylor outlined a cybersecurity landscape defined by constant adversarial adaptation, rising geopolitical uncertainty, and the accelerating impact of AI.
As organizations strengthen traditional defenses like authentication, attackers are shifting toward indirect methods such as help desk exploitation and social engineering, exposing new weak points in enterprise security. Against this backdrop, Taylor emphasized the growing importance of identity as the central control plane, the emergence of sovereign deployment models to address resilience and regulatory concerns, and the long-anticipated transition to passwordless authentication.
At the same time, AI is reshaping both offense and defense, introducing powerful new capabilities while dramatically expanding the threat surface.
Core Takeaways
Bypass Attacks Shift the Threat Landscape: As organizations strengthen front-line defenses like FIDO-based authentication, attackers increasingly exploit indirect entry points such as help desks and social engineering, targeting the weakest links rather than the most fortified systems.
Sovereign Deployment Reflects a New Risk Reality: Enterprises and governments are demanding greater control over their infrastructure due to geopolitical instability, regulatory pressure, and resilience concerns, driving interest in flexible deployment models that replicate full SaaS capabilities across on-prem, cloud, and air-gapped environments.
Passwordless Is Finally Reaching Enterprise Adoption: After years of anticipation, passwordless authentication is entering a critical adoption phase, with enterprise funding, board-level support, and mature technology converging to make widespread deployment viable within the next one to two years.
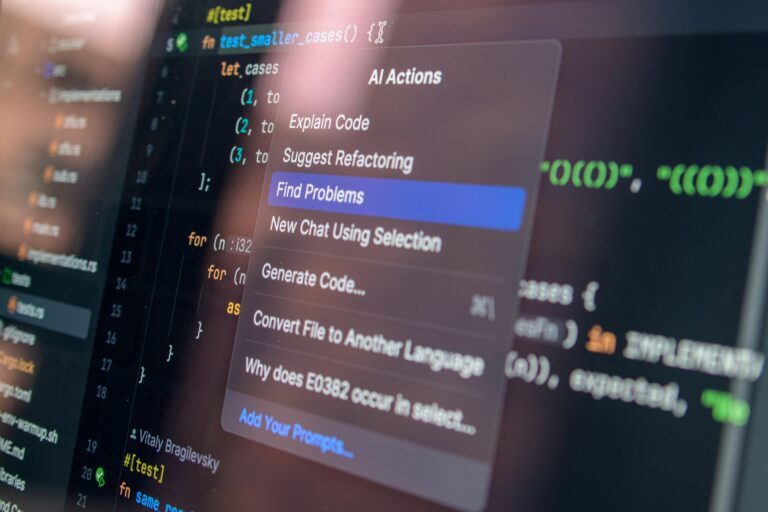
AI Redefines Both Threats and Defenses: AI is transforming cybersecurity into a data-scale problem, enabling both more efficient attacks such as low-cost phishing and more advanced defenses through automation, while also introducing new challenges around securing non-human identities and autonomous agents.
Key Quotes
The Weakest Link Is Always the Target
“We’ve just been through a phase where we strengthened the front door with things like FIDO and strong credentials. But attackers adapt. If they can’t get through the front door, they go around and break in through the window. That’s why we’re seeing the rise of bypass attacks, especially targeting help desks and using social engineering.”
“Security is like a house in a flood. The water will always find the weakest point. It’s not about whether you have strong defenses in one area, it’s about understanding where the next vulnerability will emerge. That’s the challenge, constantly anticipating where attackers will shift next.”
Control and Resilience Drive Sovereign Deployment
“The world has become a more uncertain place, and organizations are asking more ‘what if’ questions. What happens if a service goes down, or a network is disrupted? We’ve seen real-world examples where infrastructure is directly impacted by geopolitical events, and that’s forcing a rethink.”
“Sovereign deployment is about giving customers full control without compromise. It’s not a limited version of our platform. It’s full stack, deployable wherever they need it, whether that’s in the cloud, on-prem, or even in air-gapped environments. Customers want both flexibility and assurance.”
Passwordless Is Finally Within Reach
“The idea of eliminating passwords has been around for decades, but now everything is coming together. The technology is ready, enterprises understand the benefits, and it’s getting real funding and executive attention. This isn’t theoretical anymore.”
“I believe the next one to two years will be the tipping point where passwordless becomes a reality at scale. Enterprises are moving from discussion to deployment, and that’s a significant shift after years of slow progress.”
AI Creates a New Cybersecurity Frontier
“AI is both exciting and unsettling. It’s a frontier moment, a bit like the Wild West. On one hand, it gives defenders powerful new tools. On the other, it dramatically lowers the cost and complexity of attacks, making capabilities like phishing far more scalable.”
“We’re also entering a world of non-human identities, where AI agents operate inside enterprises and require the same controls as human users. Securing those identities, while also defending against AI-enabled threats like deepfakes, will define cybersecurity over the next few years.”